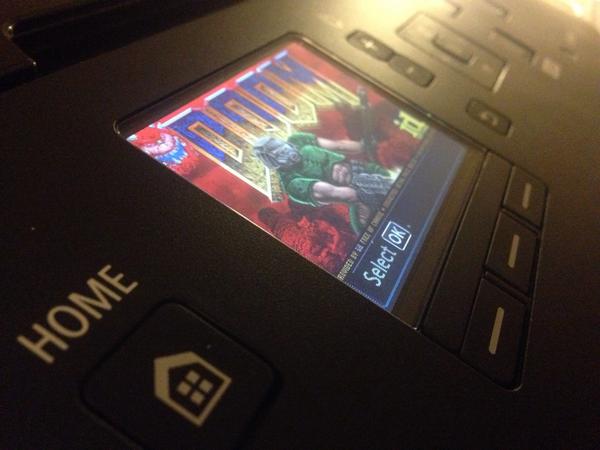
Security Consultant Hacks a Canon PIXMA Printer to Play the 1993 Video Game ‘Doom’
Context IS security consultant Michael Jordon recently demonstrated an exploitation in Canon’s PIXMA line of printers that he used to hack the device to play the 1993 video game Doom. Jordon demonstrated the exploit during 44CON 2014 in London. Specifically, the exploit only exists because of the way the device’s web interface attempts to update the firmware.
The issue is with the firmware update process. While you can trigger a firmware update you can also change the web proxy settings and the DNS server. If you can change these then you can redirect where the printer goes to check for a new firmware. So what protection does Canon use to prevent a malicious person from providing a malicious firmware? In a nutshell – nothing, there is no signing (the correct way to do it) but it does have very weak encryption.
Jordon also posted a video of the exploit in action.
photo via Context IS